LastPass Cloud Database Hack Compromises Hashed Master Passwords
Samuel Wan / 9 years ago
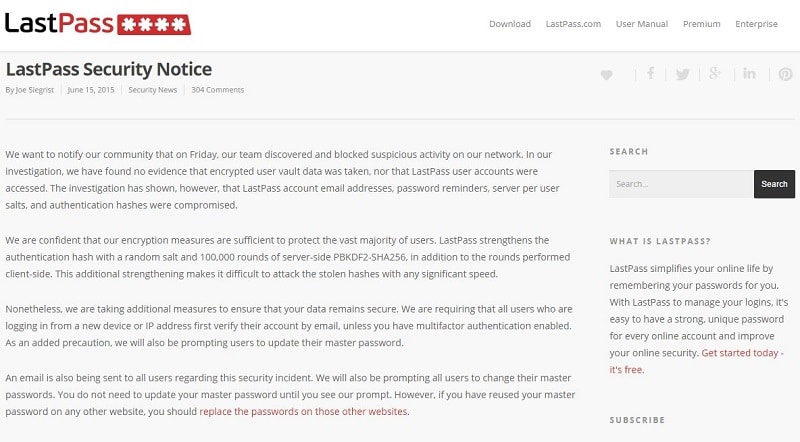
Unknown attackers have made off with LastPass account emails, password reminders and hashed user vault master passwords. CEO Joe Siegrist was quick to note that no encrypted user vault data, plaintext passwords or user accounts were accessed. This is the second security breach LastPass has faced in four years. Despite the compromise of the hashed passwords, there is no need to panic just yet.
As befitting a security firm, LastPass chose a more secure way of cryptographically hashing user master passwords. Instead of going with fast md5 or SHA1commonly used, LastPass used PBKDF2-SHA256 with a random salt and 100,000 rounds. With the addition of at least 5,000 more iterations client side, it will make it difficult to hack the hashes and obtain the password. As the encrypted users vaults were also not accessed, attackers will have to obtain that some other way as well.
LastPass is also ensuring users who are logging in from an unverified IP or device to verify via email unless they already have two-factor authentication. Given the above average security, there is no rush to change stored plaintext passwords or the master password just yet, but the earlier it can be done the better. With the difficulty of cracking a password, only those who are likely to be specifically targeted should worry.
Storing passwords anywhere is risky and even more so in the cloud as this attack demonstrated. However, user machines are already quite vulnerable and using a password manager is better than not. The stronger security offered by password manager for regular passwords is invaluable and with only 1 master password to remember, it can be more complex and longer. I know I will continue to use my cloud supported password manager but maybe I think I’ll rethink my plans to store my banking credentials. You can find the LastPass blog post on the incident here.



















