ARRIS Cable Modems Have “Backdoor in the Backdoor”
Ashley Allen / 8 years ago
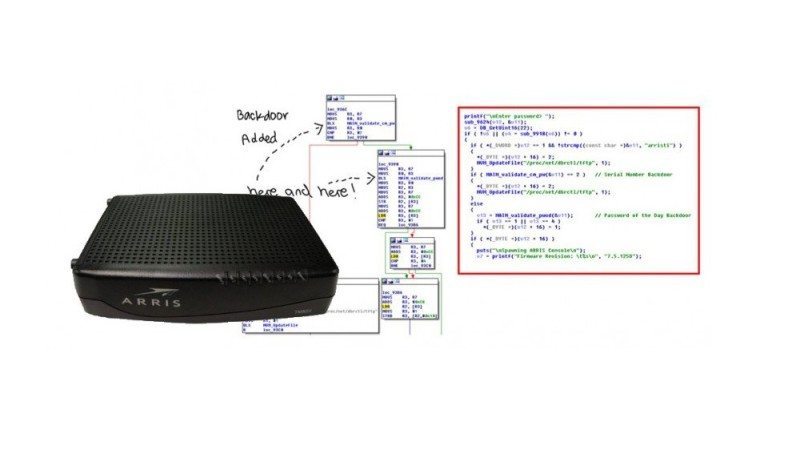
Up to 600,000 ARRIS cable modems could be vulnerable to hacks via a “backdoor in the backdoor”, according to security researcher Bernardo Rodrigues. Rodrigues, who works as a vulnerability tester for the Globo TV network in Brazil, revealed on his blog that he had “found a previously undisclosed backdoor on ARRIS cable modems, affecting many of their devices including [the] TG862A, TG862G, [and] DG860A [models].” After extending his search, Rodrigues found that up to 600,000 ARRIS modems could be affected by the vulnerability.
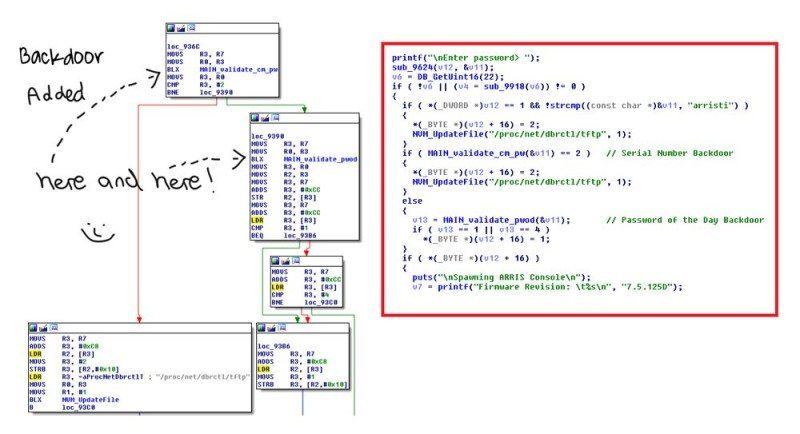
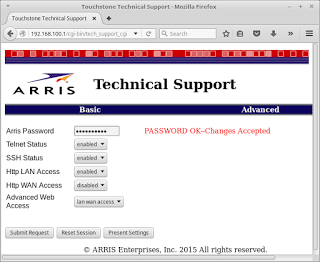
Using the default username and password of “root” and “arris”, respectively, Rodrigues was able to SSH through a hidden HTTP admin interface, where he found a system-spawned ‘mini_cli’ shell which, given the right password, would allow him into a restricted technician shell. Rodrigues cracked the ARRIS password of the day, which was generated via the last five digits of the modem’s serial number.
Rodrigues even built a Puma5 Toolchain ARMEB to help demonstrate how the backdoor operates, which he has kindly hosted on Github. He has reported how he accessed the “backdoor in the backdoor” to the vendor, which asked that he not reveal the algorithm he used to generate the password of the day. He waited until the issue had been fixed before posting his exposé. It took 65 days for the vulnerability to be corrected.



















