Flaws In UEFI Can Be Abused To Install UEFI Bootkit
Ryan Martin / 11 years ago
According to a PC World report, via Softpedia, three researchers demonstrated a UEFI vulnerability at the 2013 Black Hat conference. Andrew Furtak, Oleksandr Bazhaniuk and Yuriy Bulygin demonstrated two attack methods that can be used to bypass the secure boot to install a UEFI bootkit.
One of the attack techniques relies on a hole in the Unified Extensible Firmware Interface (UEFI). However, the particular attack requires access to the Kernel mode to launch which is difficult to do as it has the most privileges to contend with. This exploit was reported to have affected several vendors including ASUSTek though in most cases and products BIOS updates have fixed the flaw. Though the ASUS VivoBook laptop, which the presentation was given on, still has the vulnerability.
The second vulnerability which is much easier to do involves exploiting common applications such as Microsoft office, Java and Adobe Flash to bypass the Secure Boot. All security flaws revealed are recent discoveries and so vendors have been given time to address and provide details of the vulnerabilities and any fixes.
Despite the vulnerabilities of the BIOS the UEFI secure boot system is still the best way to keep computers bootkit free.
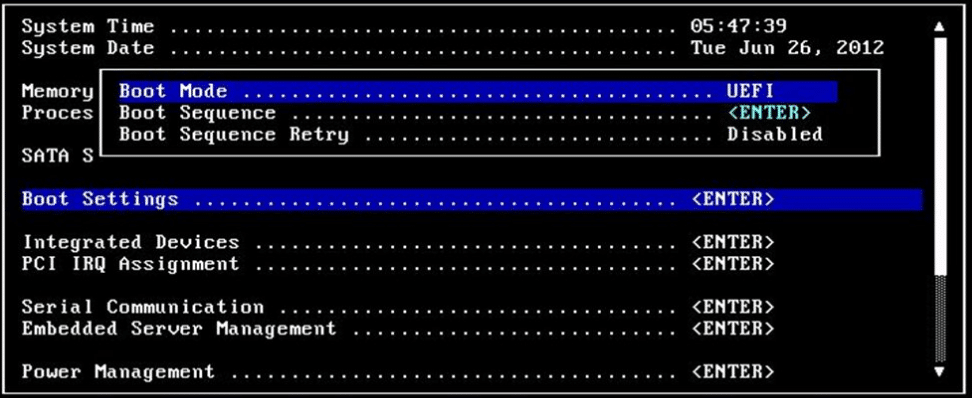
Image courtesy of Dell



















