GitHub Gets Hit by the Biggest DDoS Attack in Site’s History
Gabriel Roşu / 9 years ago

GitHub, the popular website used for projects spanning from game engines to security applications and even web app frameworks, is apparently suffering the biggest DDoS attack in the website’s history, which they believe to originate from China.
The attack appears to have started last Thursday and has all its staff working on mitigating the access problems since then. GitHub states that the attack “involves a wide combination of attack vectors,” which “includes every vector we’ve seen in previous attacks as well as some sophisticated new techniques that use the web browsers of unsuspecting, uninvolved people to flood github.com with high levels of traffic.”
“Based on reports we’ve received, we believe the intent of this attack is to convince us to remove a specific class of content,” GitHub says.
Wall Street Journal reports that GitHub’s traffic surge is based on visits intended for China’s largest search engine, Baidu. Security experts told the publication that the vast levels of traffic has paralysed GitHub over the DDoS attack’s duration.
The attack, which leads back to China, apparently targets two specific sections of GitHub. One of them is Greatfire.org, an anti-censorship organization dubbed the “Great Firewall of China”, which releases tools to help Chinese citizens bypass the county’s censorship controls, and the other links to copies of the New York Time’s Chinese language website and other banned domains.
Security specialist Anth@x from Insight Labs believes that the attack was due to HTTP hijacking by replacing some JavaScript files from Baidu with malicious ones, having Block Execution also used in order to prevent looping. The security specialist even goes further and states that non-Chinese users are now also being “weaponized” to target the country’s targets.
“In other words, even people outside China are being weaponized to target things the Chinese government does not like, for example, freedom of speech.” Anth@x posted on Insight Labs.
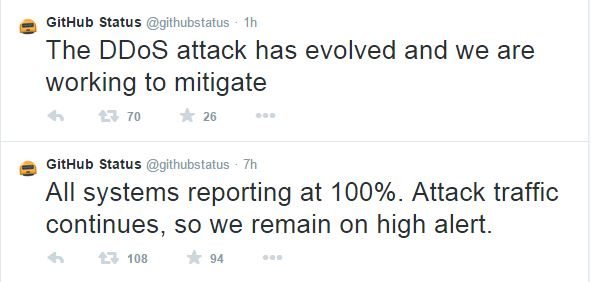
GitHub’s status updates twitter account has been keeping us updated with the attack’s status. While yesterday they reported that “all systems reporting at 100%. Attack traffic continues, so we remain on high alert.”, about an hour ago, they stated that “The DDoS attack has evolved and we are working to mitigate”.
Baidu apparently denies involvement in the attack and states that it “was not intentionally involved in any traffic redirection”.
Thank you ZDnet for providing us with this information



















