Ransomware Locks Your Android Phone Pin And Asks For Cash
Christopher Files / 9 years ago

Ransomware is akin to the booming stock market of yesteryear for hackers, the notion of locking an individual’s infected device is a powerful reality for today’s modern day connected gadgets. As such it can be no surprise that a new technique has surfaced which implements a free app on third-party app stores which changes the device’s locking PIN and then asks for $500 as a kind of screw you post it.
Technique of this ransomware.
Let’s take a look at the details; it may take a while so make yourself comfortable. Security firm ESET has detected this threat as a Android/Lockerpin.A, users have no effective way of regaining access to their device without root privileges or without some other form of security management solution installed, apart from a factory reset, but this would delete all data as a consequence.
After successful installation, this type of malware attempts to obtain user admin privileges by attempting to trick users, it does this by overlaying the activation window with the Trojan’s malicious window which pretends to be an “Update patch installation”. As the user clicks through this innocuous-looking installation they also unknowingly activate the Device Administrator privileges in the hidden underlying window.
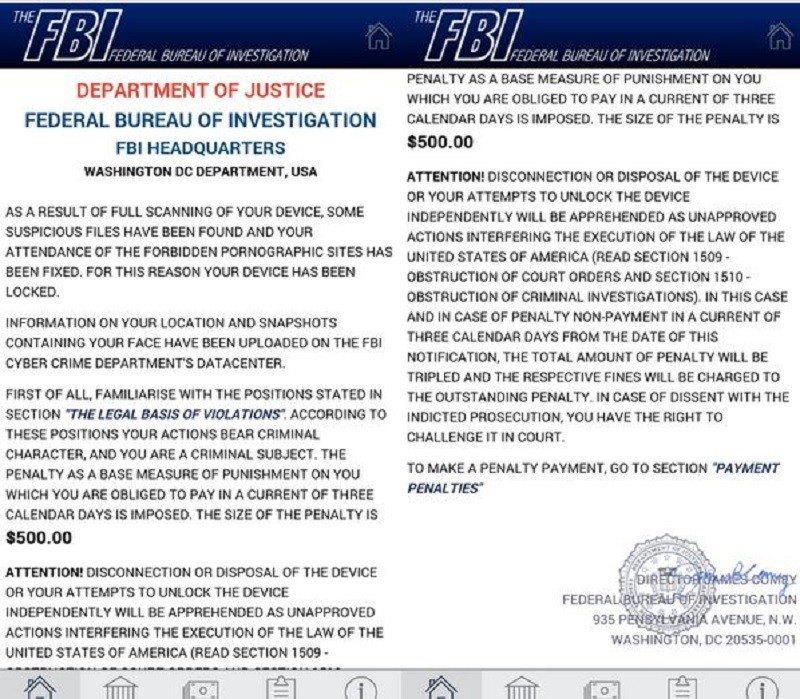
This is lethal considering the moment you click “continue” within the installation activation window, your device has fallen victim, the Trojan app has now obtained Administrator rights and has silently locked your device by setting a new PIN for the lock screen. Not long after this has happened, the user will be prompted to pay a $500 dollar ransom for allegedly viewing and harbouring forbidden pornographic material, below is a screenshot of this warning notice.
The device is then locked after the warning screen is displayed within the standard Android lock screen. The new PIN is generated randomly and not sent to the attacker. The only practical way to unlock is to reset to factory defaults.
Lockpin’s self defence mechanism part 2.
Not only does this type of ransomeware acquire device admin privileges it also stops users from attempting to deactivate Device Admin for the malware, they will fail because the Trojan will have registered a call-back function to reactivate the privileges when removal is attempted.
There’s more, this locker also attempts to kill running AV processes when the user tries to deactivate its Device Admin rights. The Trojan tries to protect itself from three mobile anti-virus applications which include ESET, Avast and Dr Web as well as the com.android.settings which prevents standard uninstallation through the application manager.
ESET state that its own self-protection mechanisms will prevent the malware from removing this vendor’s AV. Software.
Distribution of this malware
This Ransomware pretends to be an app for viewing adult/porn videos. In all cases, the application calls itself “Porn Droid”, giggity. 75% of so far infected devices have originated from the US; this is because malware coders are attempting to attack citizens of the US with the aim of collecting bigger payouts.
Unlocking the device
The only way to unlock your device without implementing a factory reset is to root your device; the user can connect to the device by ADB and remove the file where the PIN is stored. For this to work, the device needs to have debugging enabled otherwise it’s not possible (Settings -> Developer options -> USB Debugging) before using the commands
> adb shell
> su
> rm /data/system/password.key
The only crumb of comfort is that you cannot download this malicious app from the official Google Play Store, ESET recommends keeping your mobile AV software up to date if you have one. If not, be careful what you download, if you stick to official routes and be cautious of both unknown and suspicious apps which purport to be too good to be true. Back up any sensitive data and always update legitimate software, tech is becoming more advanced and so are the attackers.
Thank you eset for providing us with this information.
Image courtesy of xperiaseries



















