Siezed Megaupload Domains Hijacked By Scam Ads and Malware
Ashley Allen / 9 years ago
Megaupload domains that were seized by the US Department of Justice, as part of its legal action against company founder Kim Dotcom, have now been hijacked by scammers who are using the domain names to distribute malware and host scam adverts. Megaupload.com and Megavideo.com are now active again after the FBI lost control of the main nameserver, a happenstance that Dotcom says the DoJ and FBI should have prevented.
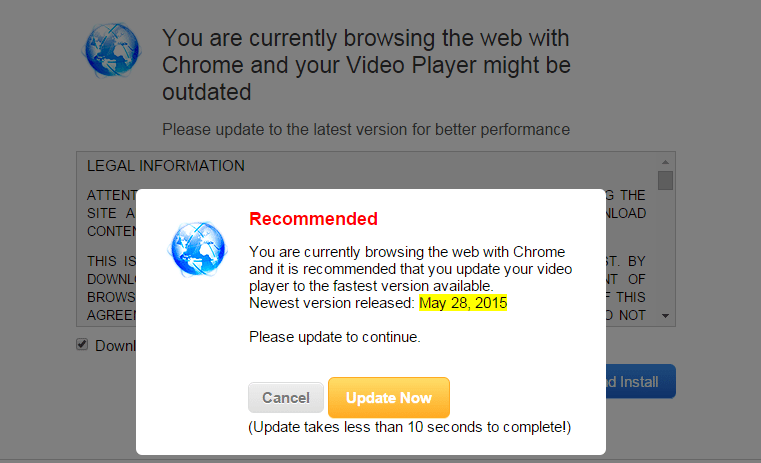
Until recently, the two domains featured a banner informing visitors that sites had been seized as part of a criminal investigation, but now they direct people to a Zero-Click ad feed that pushes malware installers and other malicious materials.
A look at the Whois records, rather suspiciously, show the nameserver as PLEASEDROPTHISHOST15525.CIRFU.BIZ:
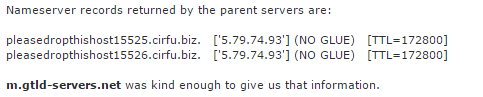
While the domains were under the control of the US government, the nameserver showed as CIRFU.NET, referring to the FBI’s Cyber Initiative and Resource Fusion Unit.
Dotcom told TorrentFreak that he believes the domain debacle to be an indictment of the DoJ’s competence, saying, “With U.S. Assistant Attorney Jay Prabhu the DOJ in Virginia employs a guy who doesn’t know the difference between civil & criminal law. And after this recent abuse of our seized Mega domains I wonder how this guy was appointed Chief of the Cybercrime Unit when he can’t even do the basics like safeguard the domains he has seized.”
“Jay Prabhu keeps embarrassing the U.S. government. I would send him back to law school and give him a crash course in ‘how the Internet works’,”
It is within the power of the FBI and DoJ to reclaim the domains with an update of the nameserver but, at last check, the two domains remain under malicious control.
Thank you TorrentFreak for providing us with this information.



















