Drive Destroying Malware Discovered
Rikki Wright / 9 years ago
Cisco Systems’ Talos Group have discovered a new malware that takes ninja operation to a whole new level. It has been dubbed Rombertik and it basically monitors everything you do on the web, including all of your personal information.
This nasty bit of software gets installed when a user unknowingly clicks on a malicious link; either from an email or off a website. The researchers reversed engineered the software to see exactly what is going on, Rombertik stays hidden in the deepest darkest part of your hard drive, cloaking itself when the user goes near and that can self-destruct if put under scrutiny from anyone; it has been known to wipe entire hard drives clean to prevent anyone learning the code.
Researchers Ben Baker and Alex Chiu kept a blog of their investigation:
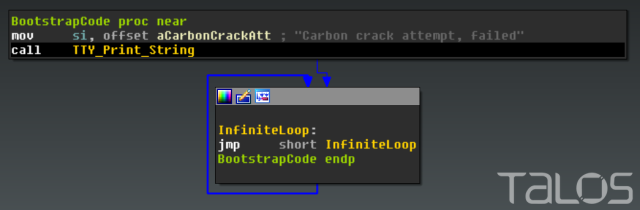
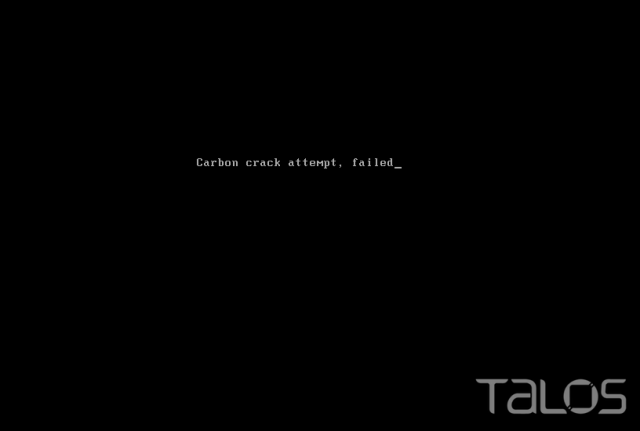
Once the unpacked version of Rombertik within the second copy of yfoye.exe begins executing, one last anti-analysis function is run — which turns out to be particularly nasty if the check fails. The function computes a 32-bit hash of a resource in memory, and compares it to the PE Compile Timestamp of the unpacked sample. If the resource or compile time has been altered, the malware acts destructively. It first attempts to overwrite the Master Boot Record (MBR) of PhysicalDisk0, which renders the computer inoperable. If the malware does not have permissions to overwrite the MBR, it will instead destroy all files in the user’s home folder (e.g. C:\Documents and Settings\Administrator\) by encrypting each file with a randomly generated RC4 key. After the MBR is overwritten, or the home folder has been encrypted, the computer is restarted.
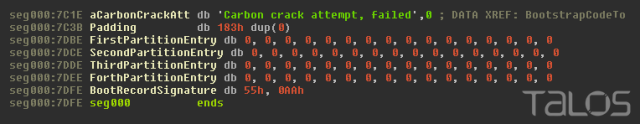
The Master Boot Record starts with code that is executed before the Operating System. The overwritten MBR contains code to print out “Carbon crack attempt, failed”, then enters an infinite loop preventing the system from continuing to boot.
The MBR also contains information about the disk partitions. The altered MBR overwrites the bytes for these partitions with Null bytes, making it even more difficult to recover data from the sabotaged hard drive.
Once the computer is restarted, the victim’s computer will be stuck at this screen until the Operating System is reinstalled:
Effectively, Rombertik begins to behave like a wiper malware sample, trashing the user’s computer if it detects it’s being analyzed. While Talos has observed anti-analysis and anti-debugging techniques in malware samples in the past, Rombertik is unique in that it actively attempts to destroy the computer if it detects certain attributes associated with malware analysis.”
The malware also has some less destructive cloaking measures, to evade sandbox tools, it writes random data to memory 960 million times; The delay from that can trip up a sandbox tool.
“If an analysis tool attempted to log all of the 960 million write instructions, the log would grow to over 100 gigabytes,” the Talos researchers explained. “Even if the analysis environment was capable of handling a log that large, it would take over 25 minutes just to write that much data to a typical hard drive. This complicates analysis.”
Well, that sounds like a nasty bit of programming. I’ll admit, I have been stung by malware a few times, most recent being around a month ago with those shopping aid ad extensions. Have you ever been snagged by malware? What are your preventative measures? Let us know in the comments.
Thank you to ArsTechnica for providing us with this information.