D-Link Inadvertently Publishes Its Private Code-Signing Keys
Christopher Files / 9 years ago
Hackers are viewed within the media and by films as master genius’s who are able to hack into protected systems with the intention of stealing a vast array of information. There is some truth in this assertion considering even multinational companies have been caught napping by cyber thieves, but, what happens if I don’t know, a tech firm accidentally publishes its private signing keys? Well, D-Link has managed to do this in what is known scientifically as stupididiotness.
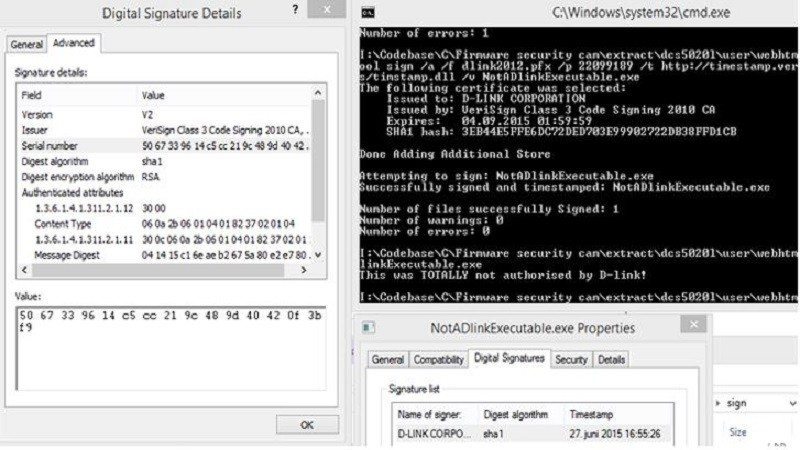
Taiwan-based networking equipment manufacturer D-Link has published its Private code signing keys inside the company’s open source firmware packages. This was spotted by a user by the username “bartvbl” who had bought a D-Link DCS-5020L security camera and downloaded the firmware from D-Link which open sources its firmware under the GPL license.
All seemed well for “bartvbl” until they inspected the source code, only to find four private keys which are used for code signing. To test this, the user-created a windows application which was able to be signed by one of the four keys which appeared to be valid. Not only this, the user also discovered pass-phrases which are needed to sign the software,
It is yet unclear if any of these keys were used in attacks by malicious third parties, meanwhile, D-Link has seen the light and has responded to this embarrassment by revoking the certificate in question and subsequently releasing a new version which does not contain any code signing keys, which is good.
Thank you tweakers via Google Translate for providing us with this information.
Image courtesy of thehackernews.



















