Synology NAS OS Vulnerable to CryptoLocker [updated]
Bohs Hansen / 10 years ago
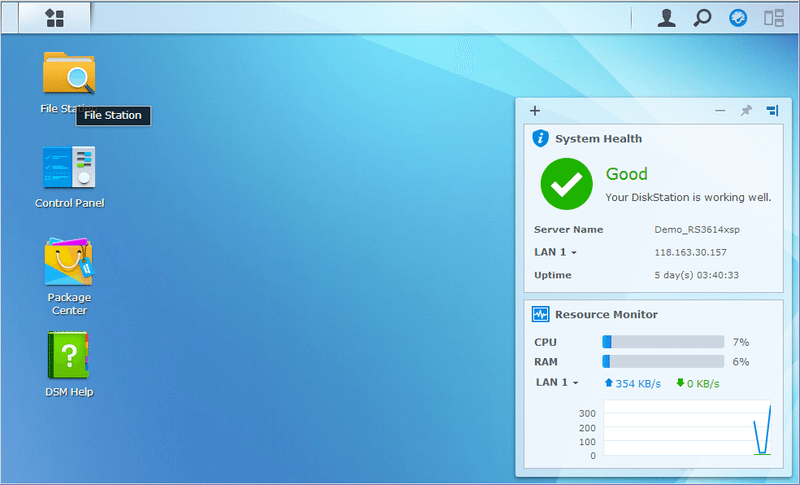
The operating system run on Synology’s NAS devices, called DiskStation Manager (DSM), is reportedly vulnerable to a CryptoLocker hack. This particular version has been dubbed SynoLocker and is holding the infected NAS devices for ransom.
The nature of how the systems get infected is still unclear, but when infected, the malware encrypts parts of the data until you pay 0.6 Bitcoins (about £208 at current rate). Decryption is promised upon payment, but there is no guarantee it will happen and that you won’t be infected again.
The company believes it to be limited to devices still running non-updated versions of DSM 4.3, they are however still investigating if the vulnerability also could infect the newer version 5.0, just in case.
While a press release is being prepared, Synology gave this emergency statement:
You may have heard by now that DSM is undergoing a CryptoLocker hack called SynoLocker – as of yesterday (08/03/14). It’s a BitCoin Mining hack that encrypts portions of data, and ransoms the decryption key for .6 BitCoin ($350). So far, it looks like the matter is localized to non-updated versions of DSM 4.3, but we are actively working on, and researching the issue to see if it also effects DSM 5.0 as well.
In the interim, we are asking people to take the following precautions:
A. Close all open ports for external access as soon as possible, and/or unplug your Disk/RackStation from your router
B. Update DSM to the latest version
C. Backup your data as soon as possible
D. Synology will provide further information as soon as it is available.If your NAS has been infected:
A. Do not trust/ignore any email from unauthorized/non-genuine Synology email. Synology email always has the “synology.com” address suffix.
B. Do a hard shutdown of your Disk/RackStation to prevent any further issues. This entails a long-press of your unit’s power button, until a long beep has been heard. The unit will shut itself down safely from that point.
C. Contact Synology Support as soon as possible at, http://www.synology.com/en-global/support/knowledge_base
[UPDATE 16:50 GMT]
Since we originally posted this, we’ve recieved an official statement from Synology via email. The problem is more limited then first thought and only affects a few software version. As also initial suggested, those with up-to-date system can feel safe from this threat.
Synology are fully dedicated to investigating this issue and possible solutions. Based on their current observations, this issue only affects Synology NAS servers running some older versions of DSM (DSM 4.3-3810 or earlier), by exploiting a security vulnerability that was fixed and patched in December, 2013. At present, we have not observed this vulnerability in DSM 5.0.
For NAS servers running DSM 4.3-3810 or earlier, and if users encounter any of the below symptoms, synology recommends they shut down their system and contact the technical support team.
- When attempting to log in to DSM, a screen appears informing users that data has been encrypted and a fee is required to unlock data.
- A process called “synosync” is running in Resource Monitor.
- DSM 4.3-3810 or earlier is installed, but the system says the latest version is installed at Control Panel > DSM Update.
For users who have not encountered any of the symptoms stated above, we highly recommend downloading and installing DSM 5.0, or any version below:
- For DSM 4.3, please install DSM 4.3-3827 or later
- For DSM 4.1 or DSM 4.2, please install DSM 4.2-3243 or later
- For DSM 4.0, please install DSM 4.0-2259 or later
It is easy to update the Disk Station Manager OS by going to Control Panel and then navigating to the DSM Update. Users can also manually download and install the latest version from Synology’s Download Center. If you notice any strange behaviour or suspect your Synology NAS has been affected by the above issue, you’re also encouraged to contact Synology at security@synology.com where a dedicated team will look into each case.
Thank you TechPowerUp for providing us with this information
Image courtesy of Synology



















